


We examine the frequency and scale of cyberattacks in the first half of 2016, and see whether security experts’ predictions were on the money at the start of the year.
Like death and taxes, few things are more certain than the annual deluge of cybersecurity breaches, which shows no sign of abating despite the best efforts of the ‘good guys’ — the security industry, CSIOs, government bodies, ‘white hat’ hackers, academics and others. Another fixture in the tech calendar is a spate of articles around the turn of every year that attempt to predict how the cybersecurity landscape will change over the next 12 months.
At the beginning of 2016, ZDNet’s sister site Tech Pro Research examined 244 cybersecurity predictions for 2016 from 38 organisations, and assigned them among 22 emergent categories (occasionally splitting a prediction among two or three categories). The results were as follows:
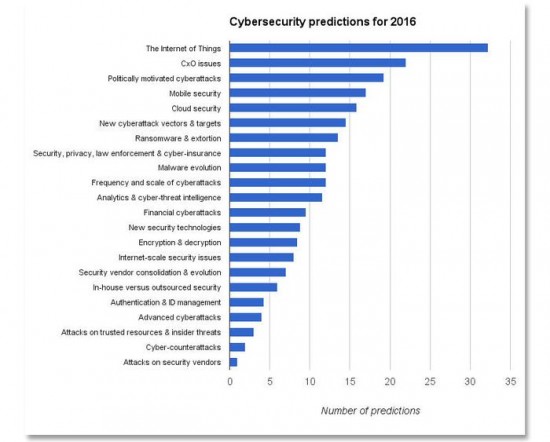
Predictions from: A10 Networks, Appriver, AT&T, BAE Systems, Blue Coat, DataVisor, DomainTools, Experian, FireEye, Forrester, Fortinet, Hexis Cyber Solutions, HyTrust, IBM, Imperva, Kaspersky, Lancope, Lieberman Software Corporation, LogRhythm, McAfee, MWR Info Security, NSFOCUS Global, OpenSky/TUV Rheinland, Ovum, Palerra, PCI Security Standards Council, Proofpoint, Raytheon/Websense, RSA, Seculert, Sophos, Symantec, Technology Business Research, ThreatStream, Trend Micro, Varonis, Vectra Networks, ZScaler
Image: TechProResearch
Now that we’re well over halfway through the year, it’s worth examining how the pundits’ predictions are panning out: are we seeing an explosion in IoT-related incidents, for example — as the above graph suggests — or are some less-heralded cybersecurity issues dominating the headlines?
But first, let’s look at some general trends.
Breach Level Index data
Security firm Gemalto’s Breach Level Index (BLI) is a database that tracks publicly disclosed breaches across the globe, measuring their severity via a multidimensional index based on factors including the number of compromised records, the source of the breach and the type of breach.
The index runs from 1-10 on a (base 10) logarithmic scale, as in the indices for volcanoes and earthquakes, so a score of 7 is ten times more severe than a score of 5.
These BLI scores can be mapped to a simple 5-point scale, ranging from Category 1 (“A breach with no material effect. Less than 1000 records. Notification required but little damage done.”) to Category 5 (“A breach with immense long-term impact on breached organization, customers and/or partners. Very large amount of highly sensitive information lost [usually 10-100+ million records]. Massive notification process. Potentially existential financial loss for breached organization in remediation and related costs. Use of lost sensitive information seen.”).
Here are the breaches for the first half of 2016 on this 5-point scale:
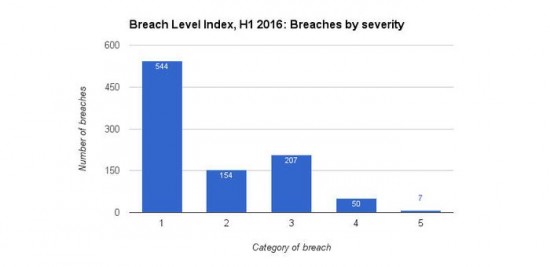
Data: Gemalto Breach Level Index / Image: ZDNet
The majority of H1 2016′s publicly disclosed breaches — 544 out of 962, or 56.5% — fall into the “Little damage done” Category 1, but there are 50 Category 4 breaches and seven Category 5 ones.
The latter are headed by the 40 million records stolen from Fling.com, an adult dating website, and put up for sale on the Dark Web.
The 962 breaches in H1 2016 resulted in 537 million compromised records, including 26 breaches with over a million records affected. However, the number of compromised records was unknown in 53 percent of the breaches.
Comparable figures for the whole of 2015 are: 1,673 breaches; 707 million compromised records; 46 breaches with over a million affected records; and 47 percent of breaches with unknown numbers of compromised records. Clearly, there’s no apparent let-up in the frequency and scale of cybercrime.
What are the sources of all these security breaches? Here’s the BLI data going back to H1 2014:
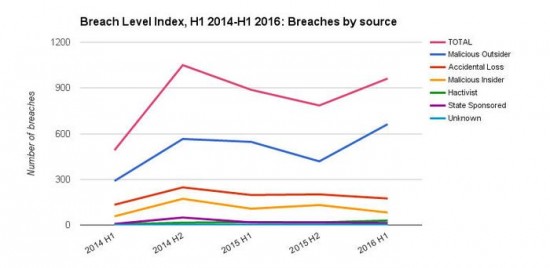
Data: Gemalto Breach Level Index / Image: ZDNet
Malicious Outsiders are consistently the number-one source of breaches over the last two years, followed by Accidental Loss and Malicious Insiders. Hacktivist and State Sponsored breaches remain at low levels compared to this trio of ‘traditional’ sources.
This general pattern also holds when we look at just the biggest breaches (Category 4 and 5) reported in the first half of this year:
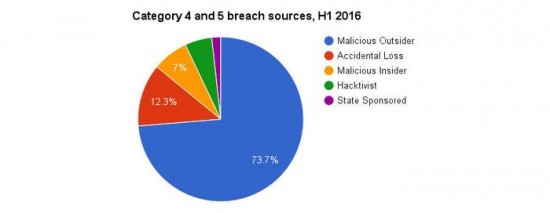
Data: Gemalto Breach Level Index / Image: ZDNet
As far as targeted industry sectors are concerned, healthcare leads the way in H1 2016 (as it has done for the past two years):
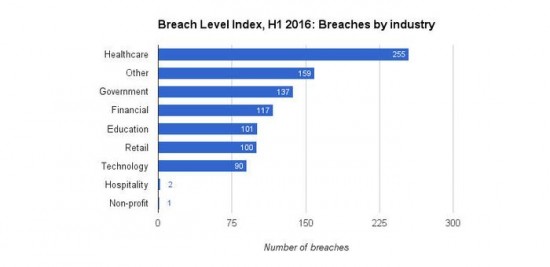
Data: Gemalto Breach Level Index / Image: ZDNet
By region, the overwhelming majority — 757 out of 962 (79%) — of reported H1 2016 breaches occurred in North America. Bear in mind, though, that the stringency of reporting regulations vary around the world.
So far, then, 2016 appears to be ‘business as usual’ so far as large-scale cybersecurity patterns are concerned.
2016 predictions so far
Let’s look at some the top prediction categories from the turn-of-the-year articles examined by Tech Pro Research (TPR) and see how the pundits have performed so far.
The Internet of Things
The fact that so many predictions for 2016 concerned the IoT — and the ‘industrial’ IoT in particular — is little surprise, given the prominence of the subject in recent years and the steady rise in IoT-related security incidents.
ICS-CERT (Industrial Control Systems Cyber Emergency Response Team) documents industrial IoT incidents in the US, and has seen a more than seven-fold rise since 2010:
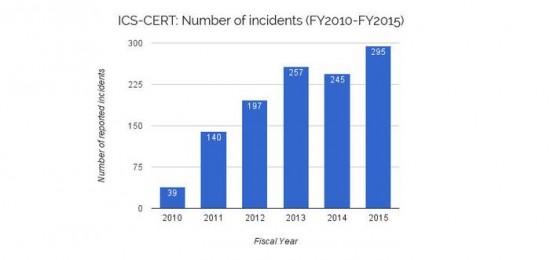
Data: ICS-CERT / Image: ZDNet
It will be interesting to see what the figures for FY2016 (Oct 2016-Sep 2016) look like, in due course. In FY2015, ICS-CERT found that Critical Manufacturing was the most attacked sector, ahead of Energy (the number-one target the previous year), with spear-phishing the most prevalent identifiable initial infection vector.
ICS-CERT noted that in 2015 it “responded to a significant number of incidents enabled by insufficiently architected networks, such as ICS networks being directly connected to the Internet or to corporate networks, where spear phishing can enable access.”
Spear phishing and a lack of ‘air gapping’ between industrial and business networks were both involved in one of the most widely reported IoT incidents so far this year — the downing of Ukraine’s power grid.
Incidents like the Ukraine power grid attack, and those on Japan’s critical infrastructure described in Cylance SPEAR’s February Operation Dust Storm report, are often attributed to nation states. Several pundits also noted the likelihood that terrorist groups will target the industrial IoT.
Other IoT security predictions for 2016 centred on connected cars, smart homes, wearables, medical devices and drones.
Trend Micro’s prediction that “At least one consumer-grade smart device failure will be lethal in 2016″ came to pass in May when a Tesla Model S’s autopilot failed to detect a white tractor trailer in challenging lighting conditions, leading to a fatal collision. This was a malfunction rather than a hack, but there have been plenty of proof-of-concept demonstrations of hacks on connected cars.
A large-scale attack on the IoT was recently revealed in a Level 3 Threat Research Labs report describing a family of malware that infected around a million internet-connected devices — mostly cameras and DVRs — for the purpose of creating DDoS (Distributed Denial of Service) botnets.
CxO issues
Several security experts noted the rise of cybersecurity from an IT-level issue to a boardroom concern, predicting an expanded role for CISOs (Chief Information Security Officers), in particular, in 2016.
Another prediction, from Trend Micro, that less than 50 percent of organisations will have a Data Protection Officer (DPO) — a requirement of the EU General Data Protection Regulation, adopted in April — in place by the end of 2016 looks likely to hold, given that a recent study estimated that some 28,000 DPOs will need to be recruited (24,000 in the private sector, 4,000 in the public sector) before the GDPR comes into force in May 2018.
The UK’s ‘Brexit’ vote in June may have muddied the data protection waters, but it’s likely that companies wanting to do business in the EU post-Brexit will still have to adhere to GDPR rules.
An ongoing cybersecurity skills shortage in 2016, cited by both Blue Coat and Vectra Networks in the TPR roundup, is supported by data from ESG’s 2016 IT spending intentions survey, which found that 46 percent of organizations claim that they have a problematic shortage in this area (up from 28 percent in the 2015 survey):
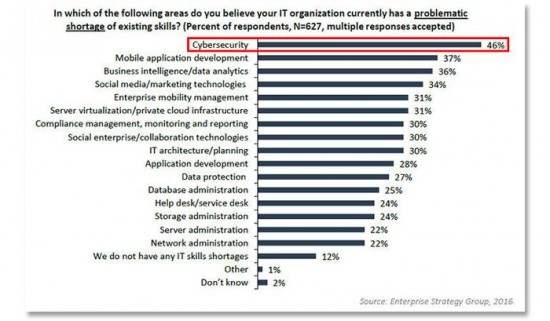
Image: Enterprise Strategy Group (ESG)
ESG went so far as to describe this finding as “a state of emergency”; the survey also found that one-third of respondents have the biggest need for cloud security specialists.
Most security breaches exploit human frailties at some point or other, usually in the early stages of network access, which is why several pundits in the TPR roundup stressed the need for CIOs to educate their user populations on good security practice in 2016 — “You can’t patch users but you can educate them,” as Varonis put it. Given that accidental loss remains the second highest source of breaches after malicious insiders (see earlier), this seems eminently sensible.
Another Varonis prediction for 2016, that “At least five more C-level executives will be fired because of a data breach,” will take more time to play out. However, if past form is any guide, more CxOs will indeed walk the plank this year following high-profile breaches at their organisations.
Politically motivated cyberattacks
The main political event of 2016 is the ongoing (and to many outside observers never-ending) U.S. presidential election campaign, and security experts including Varonis, Experian and Raytheon were alert to the hacking possibilities at the turn of the year.
And so it has proved, with the theft — and subsequent exposure on WikiLeaks in July — of some 20,000 emails and 8,000 attachments from the Democratic National Committee (DNC). The DNC breach, claimed by a hacker known as ‘Guccifer 2.0′, has been attributed to Russian intelligence groups — an aspersion denied by the Russian government.
We’ve already mentioned cyberterrorism in the context of critical infrastructure IoT hacks, and several pundits noted the possibility of increased activity in this area. Security experts also foresaw an increased incidence of state-sponsored and hacktivist attacks during 2016, although this has yet to show up convincingly in the Breach Level Index figures examined earlier.
However, leading cybersecurity commentator Bruce Schneier has recently linked an increased frequency, persistence and complexity of DDoS attacks in 2016 to the activities of nation states.
A note of optimism in this area was provided by LogRhythm, which predicted a rise in ‘ethical hacking’ in 2016: “More organizations, like Anonymous, will be leaving the dark side and hacking for the public good.
They are more motivated by the notoriety and publicity on social media than for financial gain.” So far this year, though, the main hack attributed to Anonymous was the attack on the Philippines Commission on Elections in March, which was not noticeably philanthropic.
Mobile security
The rise in mobile payment systems such as Apple Pay, Android Pay and Samsung Pay resulted in several security-related predictions at the turn of the year, exemplified by Raytheon, which noted that “Mobile wallets and new payment technologies will introduce additional opportunities for credit card theft and fraud.”
In March, researchers demonstrated that stolen credit card details (easily obtainable on the ‘dark web’) could be uploaded to Apple Pay and security checks from some banks evaded — loopholes that were not found in either Google’s or Samsung’s systems. Nevertheless, IT governance body ISACA believes that the inherent advantages of mobile payment systems — including tokenization, device-specific cryptograms and two-factor authentication — will reduce risks and increase consumer confidence over time.
Back in December, Sophos asked “Will 2016 be the year iOS malware goes mainstream?”. While Android remains far ahead of Apple’s walled-garden mobile OS in terms of the volume of malware, iOS has certainly seen plenty of security-related headlines this year — most notably around the recently discovered trio of zero-day vulnerabilities nicknamed ‘Trident’ by security researchers Lookout and Citizen Lab.
Trident is used in a sophisticated spyware product called Pegasus, which Citizen Lab has identified as the work of a secretive Israeli company called NSO Group.
Elsewhere in the iOS ecosystem, CERT UK and Lookout noted a “huge spike” in malicious activity during the latter half of 2015 thanks to SDK-exploiting malware such as XcodeGhost, resulting in a heightened background level through Q1 2016:
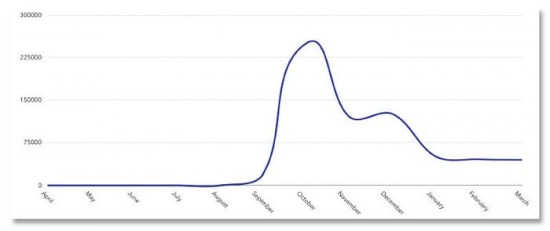
Image: CERT UK/Lookout
Although iOS is clearly vulnerable to sophisticated targeted attacks and malware introduced via the App Store, Android remains the more generally exposed platform, as this chart from the aforementioned CERT UK/Lookout report shows:
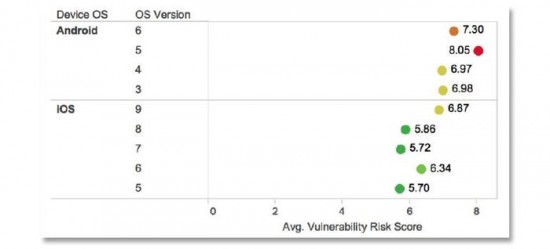
Image: CERT UK/Lookout
Mobile malware is certainly still on the increase. In Q1 2016 alone, CERT UK saw 48 percent of the full-year 2015 amount of unique mobile malware samples, broken down as follows: chargeware (31%); adware (26%); trojans (20%); riskware (15%); spyware (7%); other (1%).
Finally, DomainTools may have been prescient in December when predicting “A rise in botnets running on mobile devices…we believe that 2016 will see an inflection point, with a marked increase in mobile botnet activity.”
This year has seen the discovery by Check Point of the Viking Horde malware that infects Android phones via Google Play apps, and also the first trojan that uses rogue Twitter accounts rather than traditional command-and-control (C&C) servers to co-ordinate infected devices.
Cloud security
As companies increasingly store ever more valuable data in the cloud, so the ‘bad guys’ will inevitably follow. That’s why, back in December, Blue Coat expected to see “An increase in breaches of cloud services” in 2016, with hackers using credentials to cloud services as a major attack vector. Furthermore, said Blue Coat, “social engineering tactics will focus on mimicking cloud login screens to gain credentials.”
An important point here is that credential theft is more common than breaches of the cloud services themselves, which is why ThreatStream predicted that 2016 would be the year when “credential exposures reach a tipping point that causes some major cloud providers to force multi-factor authentication for all users.”
DataVisor also drew attention to the use of cloud services to launch cyberattacks:
“Businesses and consumers are not the only ones moving to the cloud. In 2016, we expect to see the continued migration of cyber attack infrastructure to the cloud, as cloud services become more pervasive and cost-effective. Cloud services such as AWS, Azure and Google Cloud are already victims as fraudsters register a massive number of free, trial accounts and use their computation infrastructure to conduct attacks.”
Other notable cybersecurity trends in 2016
Beyond the top five trends identified in Tech Pro Research’s January article, ransomware — which came in at number seven — has had a lot of visibility so far this year.
Hospitals and other medical institutions have been a particular focus for ransomware attacks this year, mostly targeted at patient records and other vital data. We’ve yet to see ransomware targeted at a “medical device or wearable”, as predicted by analyst firm Forrester, but the likelihood remains high that this will happen at some point.
Vectra Networks’ prediction that 2016 would see ransomware “focus more on holding enterprise assets hostage and less on individuals,” is supported by a recent report from Malwarebytes, which found that nearly 40 percent of businesses surveyed (from the US, Canada, the UK and Germany) experienced a ransomware attack in the last year, with over a third of affected enterprises losing revenue, and one in five (20%) having to cease business completely.
Encryption — number 14 in TPR’s prediction list — has had a lot of airtime this year, thanks mainly to Apple’s well-publicised spat with the FBI over the encrypted contents of one of the San Bernardino shooters’ iPhones.
A specific encryption-related prediction, from A10 Networks, that “attacks hidden in SSL traffic will exceed attacks in clear text”, has recently been followed up with a survey (conducted in partnership with the Ponemon Institute). Key findings included 80 percent of organisations (from North America and Europe) suffering cyberattacks in the past year, 41 percent of which used malware hidden in SSL traffic to evade detection.
Only 36 percent of respondents believed they could detect malicious SSL traffic, which is likely to increase (both inbound and outbound) over the next 12 months. The performance hit involved in decrypting and inspecting SSL traffic was the overwhelming concern for the organisations surveyed.
Finally, although analytics and cyber-threat intelligence made a good showing at the turn of the year, making number 11 in TPR’s chart, we might have expected more specific predictions about the use of AI and machine learning in cybersecurity. As a specialist in this area, it’s no surprise that Vectra Networks believed “organisations will realise that algorithms — not Big Data — are the key to detecting and mitigating active cyber attacks.”

DARPA’s Cyber Grand Challenge (CGC) in August pitted automated cybsersecurity systems against custom, never-before-analysed software laden with bugs.
Image: DARPA
Perhaps the most interesting AI/cybersecurity event so far this year was the DARPA Cyber Grand Challenge (CGC) at this year’s DEF CON/Black Hat conference in Las Vegas.
Designed to foster the development of advanced, autonomous systems that can detect, evaluate and patch software vulnerabilities before the bad guys can exploit them, the CGC involved seven competing teams including white-hat hackers, academics and private-sector cybersecurity experts. The winning team, Pittsburgh PA-based ForAllSecure, took home a $2 millon prize.

